Distributed systems do not fail cleanly.
They fork.
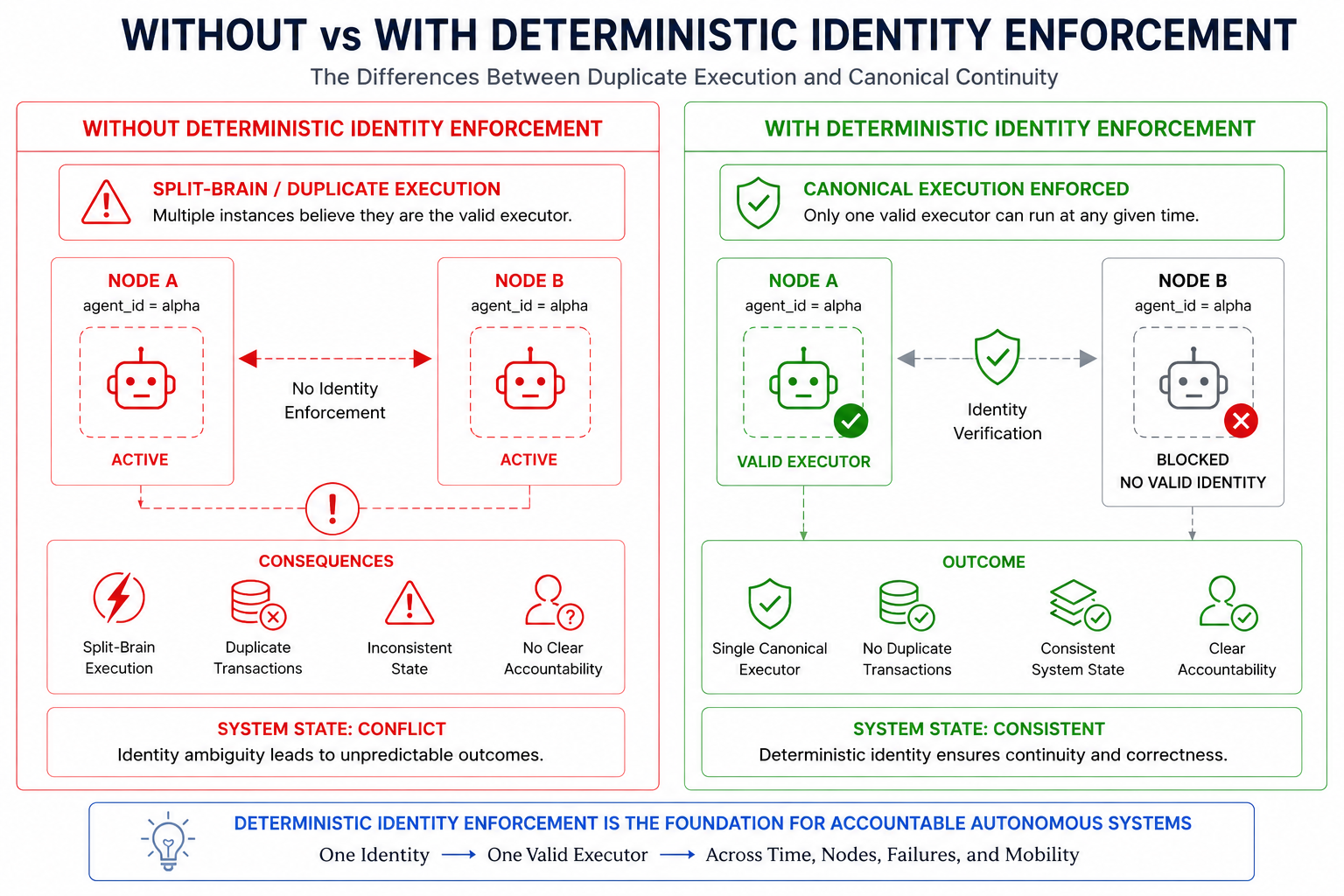
After a crash, restart, or network partition, systems often produce multiple concurrent instances of the same logical entity — each believing it is correct.
This leads to:
As autonomous systems expand into edge environments such as 5G RAN, this problem becomes critical.
This Phase 2 research validation introduced and tested a different approach:
A system model designed to ensure that a single canonical identity persists across time, regardless of failure, migration, restart, or network disruption.

In conventional distributed systems:
There is no guarantee that only one valid executor of an identity exists after failure.
Instead, distributed systems typically rely on:
These mechanisms coordinate state.
They do not enforce identity singularity.
This research explored a different primitive:
Identity can be:
This enables:
→ One Valid Executor
→ Across Time
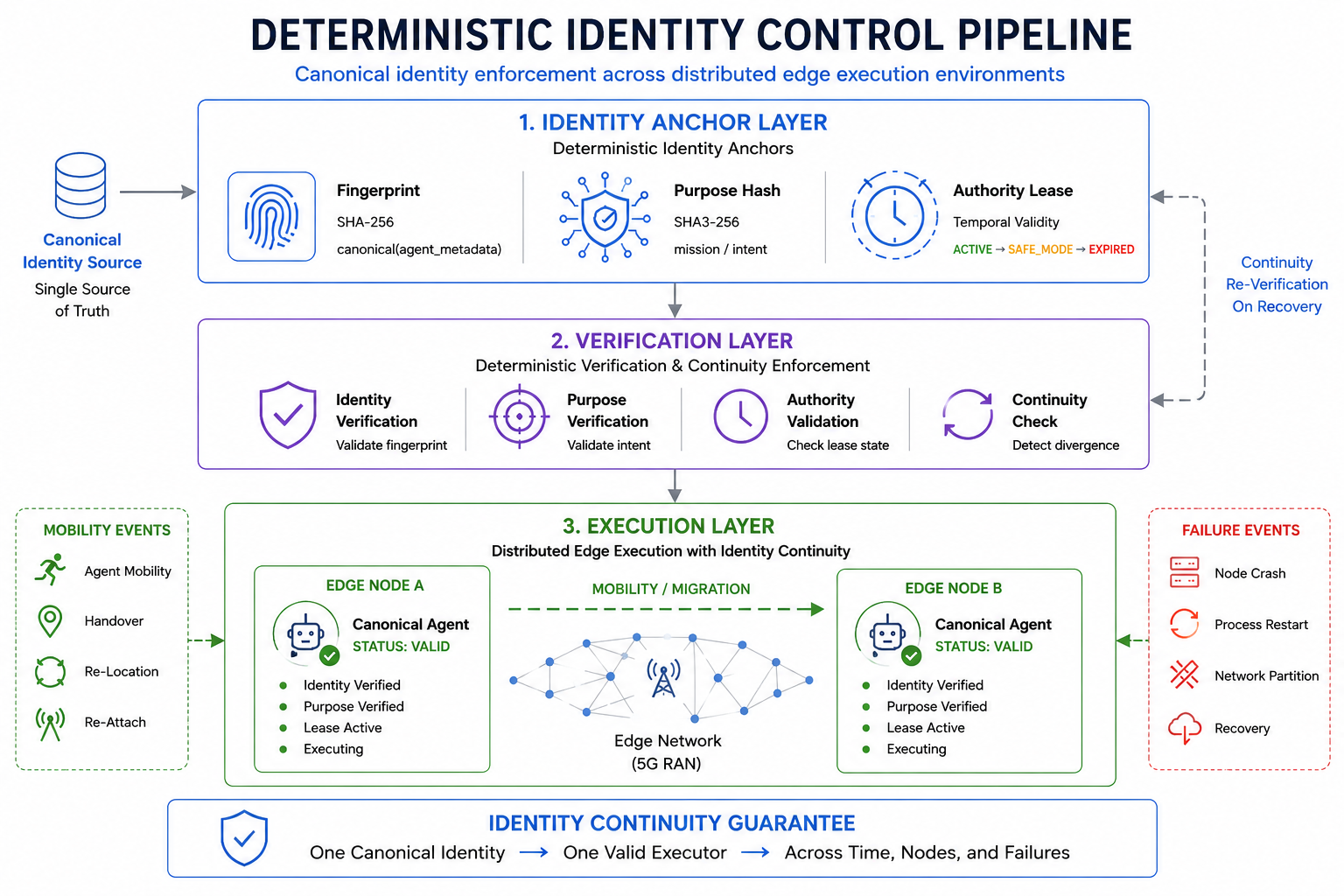
The system introduced a deterministic identity pipeline:
Identity Anchor
↓
Verification
↓
Execution
At runtime, agents operated across distributed edge nodes while maintaining:
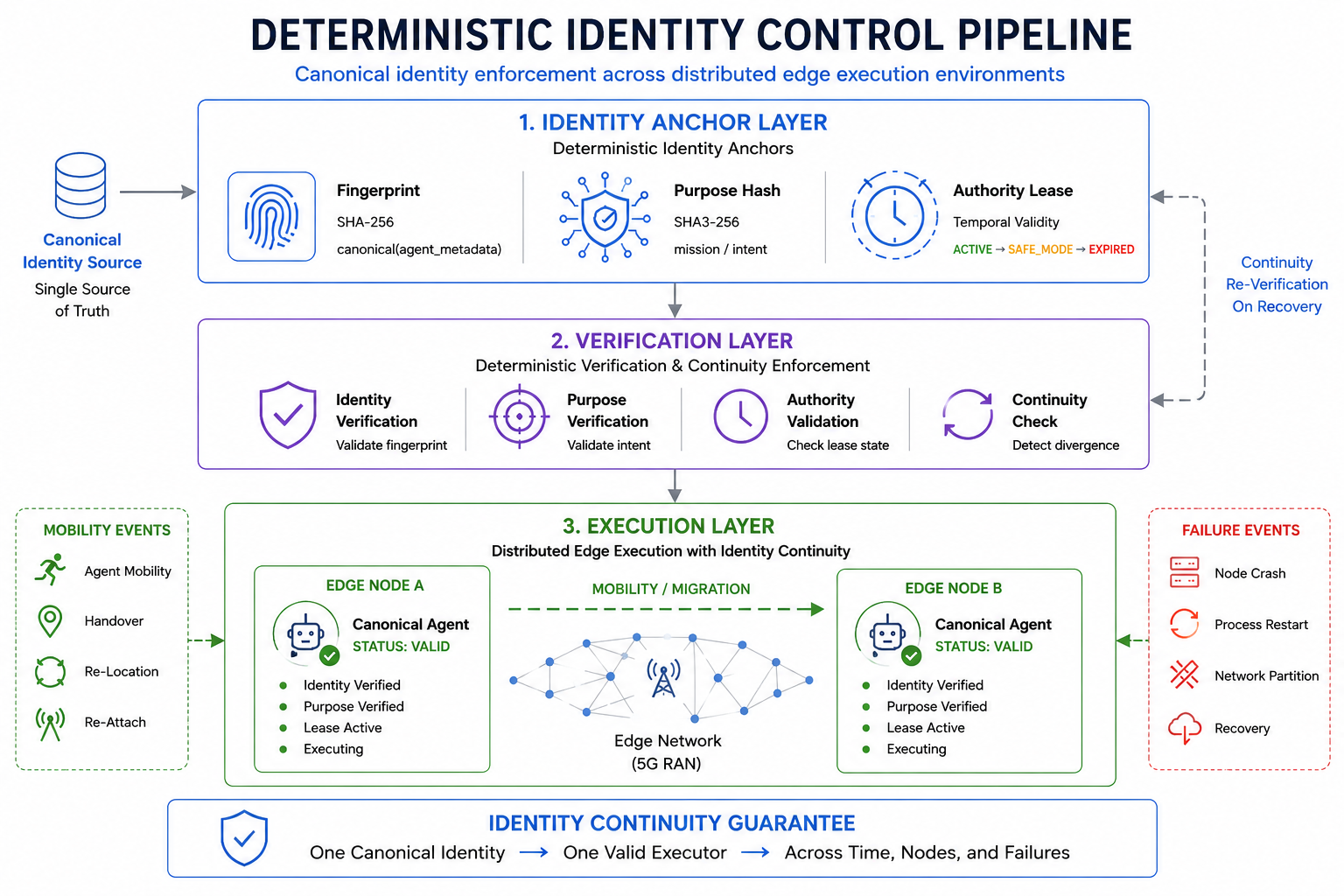
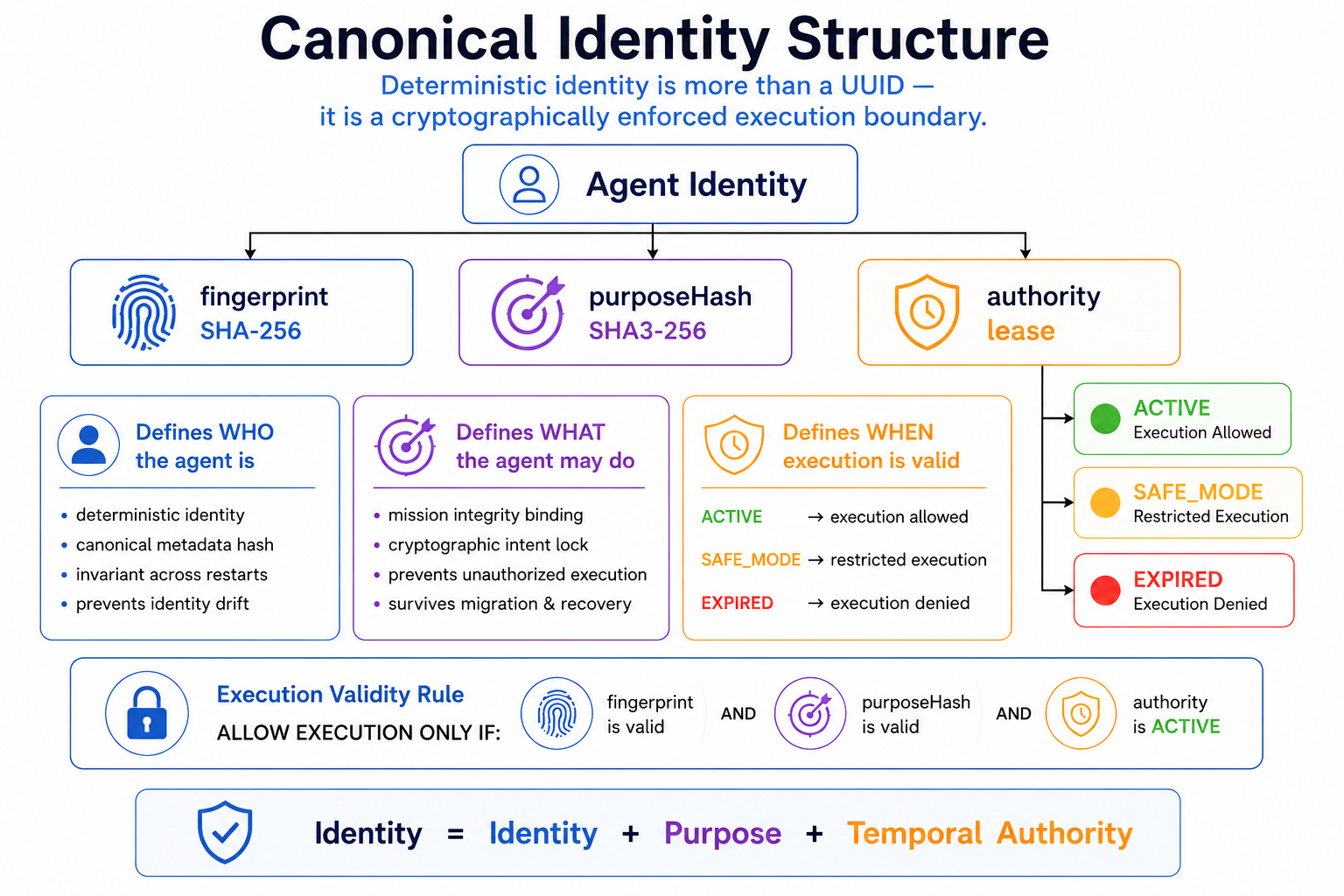
Each agent was defined using two independent cryptographic anchors.
A deterministic fingerprint derived from canonical metadata:
SHA-256(canonical(agent_metadata))
This defines:
who the agent is.
A cryptographic binding of mission or operational intent:
SHA3-256(mission)
This defines:
what the agent is authorized to do.
Execution authority operated through a lease-based state model:
ACTIVE → SAFE_MODE → EXPIRED
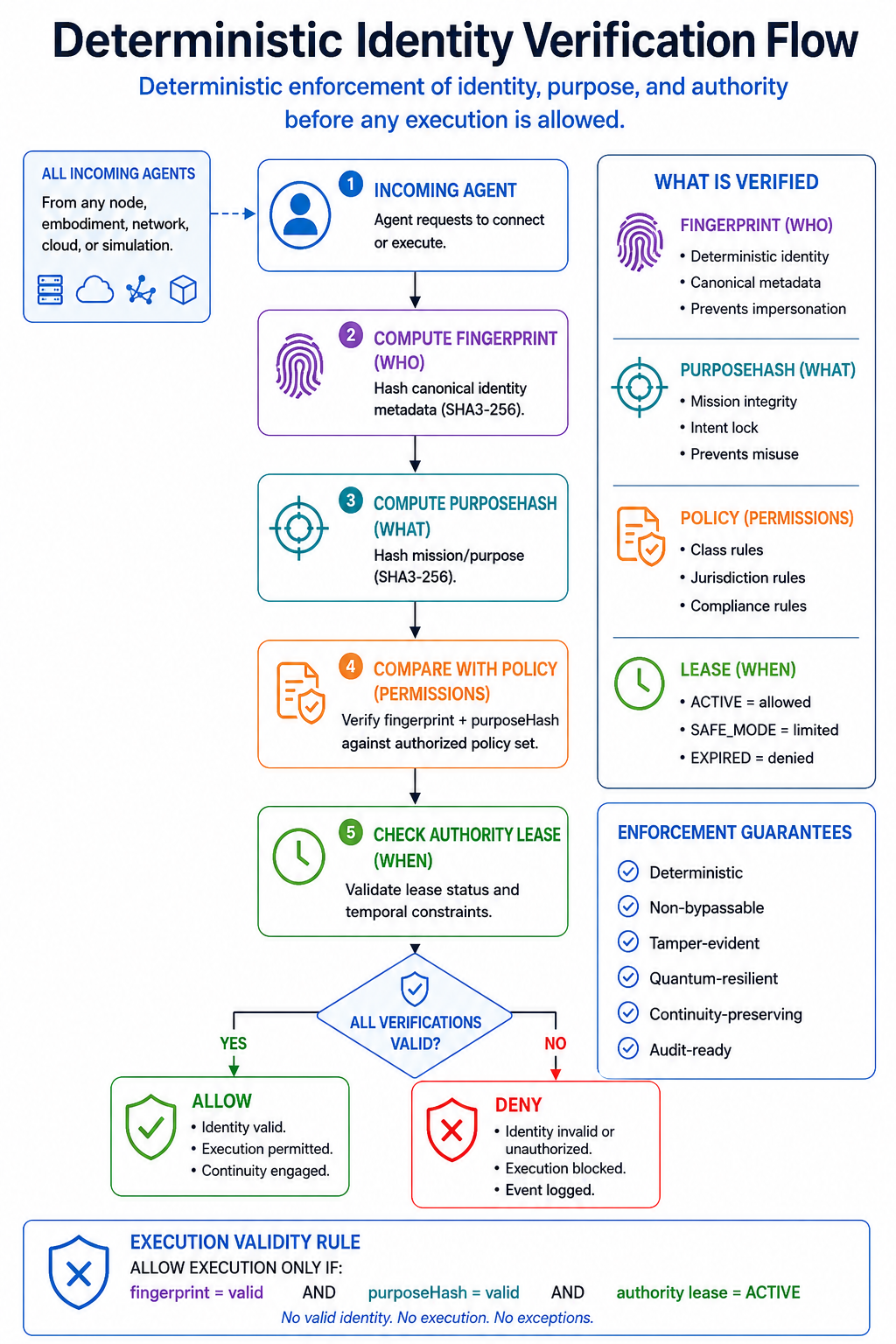
Execution was permitted only when:
Validation was conducted within a simulated 5G NR Radio Access Network environment using:
The environment simulated:
The system was evaluated under the following conditions:
Each scenario tested whether canonical identity continuity could persist across lifecycle disruption.
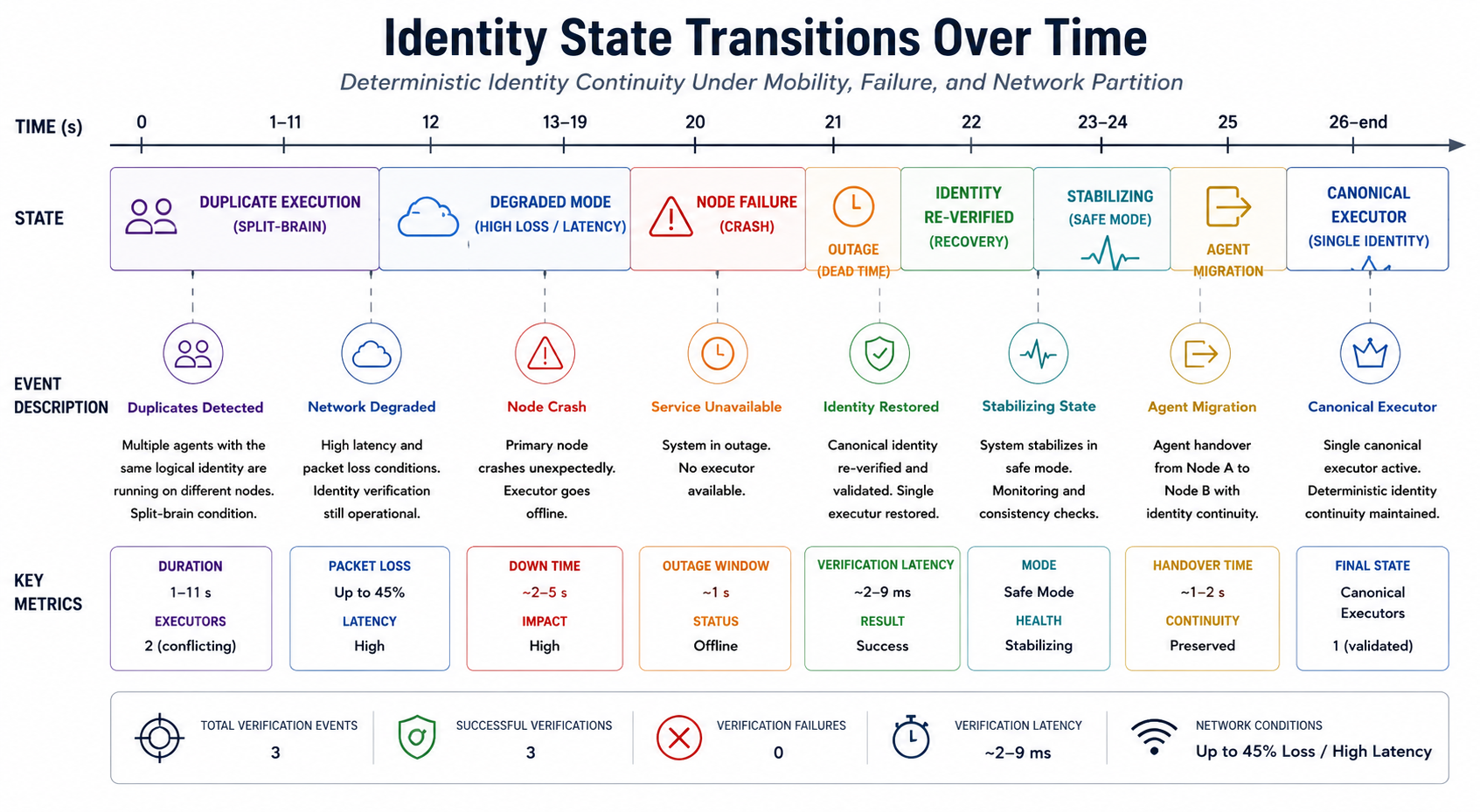
Across all tested lifecycle events:
Identity continuity remained stable under degraded network conditions including:
Identity continuity remained invariant even under severe network degradation.
This demonstrated an important architectural separation:
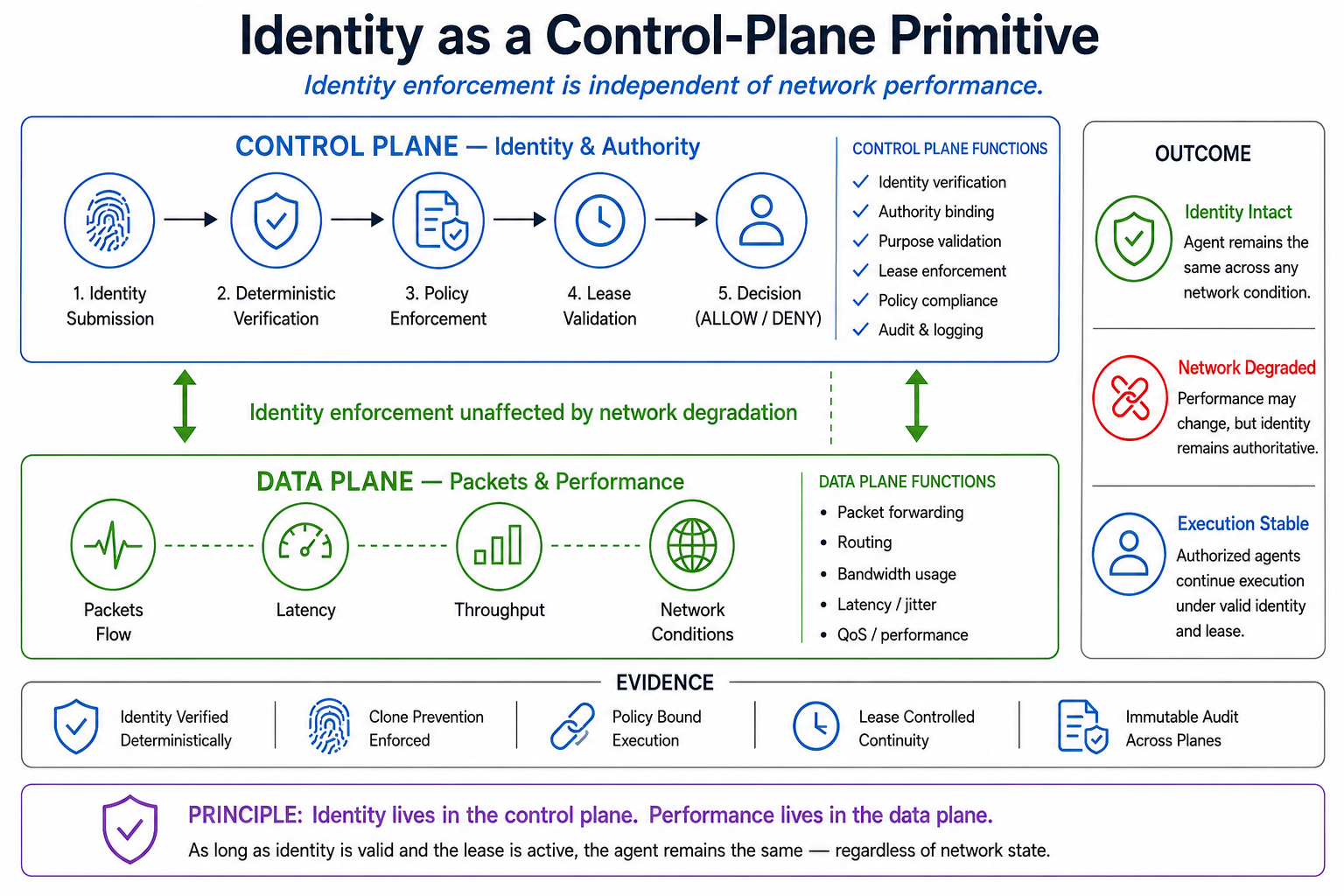
The system generated a full NetAnim simulation replay showing:
The replay visually demonstrated the transition from:
to:
During execution attempts, identity verification occurred deterministically before authority was granted.
Verification flow:
This ensured only the canonical executor could continue execution.
This Phase 2 validation demonstrated that:
This work did not attempt to demonstrate:
Those are:
This validation focused specifically on:
As systems evolve toward:
the cost of identity ambiguity increases significantly.
Without deterministic identity:
Deterministic identity continuity establishes identity as:
a control boundary,
not merely metadata.
This shifts distributed systems from:
identity as a label
to:
identity as an enforced property of execution
This Phase 2 validation established the foundational deterministic identity continuity model within simulated distributed 5G edge environments.
Subsequent ACELOGIC™ infrastructure development expanded these concepts into:
The current ACELOGIC™ infrastructure architecture builds upon the deterministic continuity principles validated in this Phase 2 research environment.
There is no system-level accountability without canonical identity.