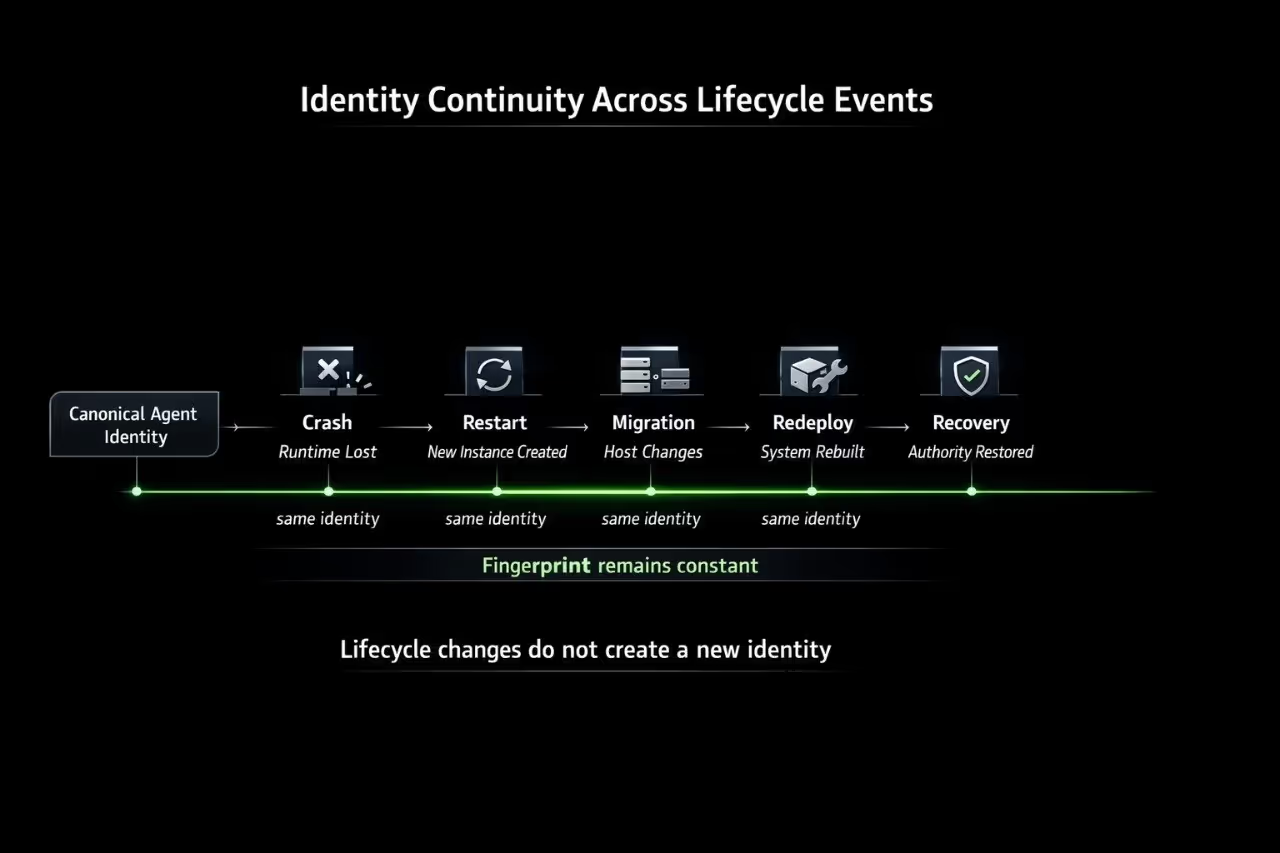
IDENTITY. CONTINUITY CONTROL PLANE
THE IDENTITY AND CONTINUITY LAYER
FOR AUTONOMOUS SYSTEMS
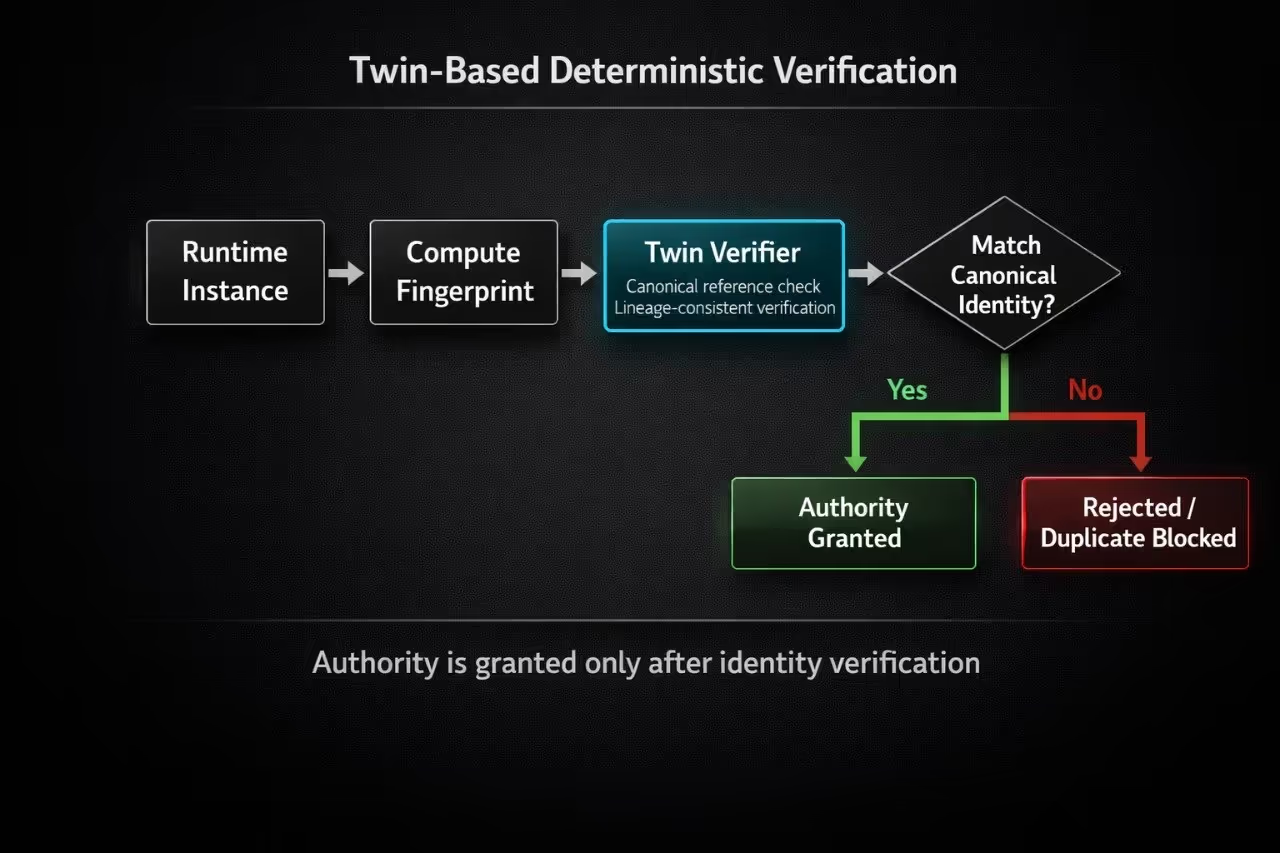
It provides deterministic identity, lifecycle continuity, and governance enforcement for agents operating across distributed environments.
.avif)

.avif)







.avif)
.avif)
